Just showing you how my Envisalink system works. I'm not sure if you are using the same system for the docker, but hopefully this message will help you debug and get it working.
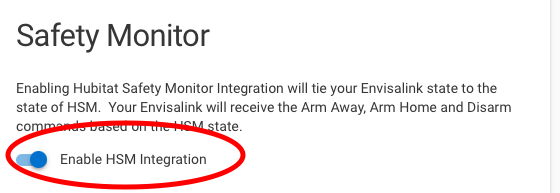
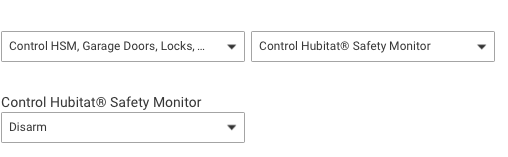
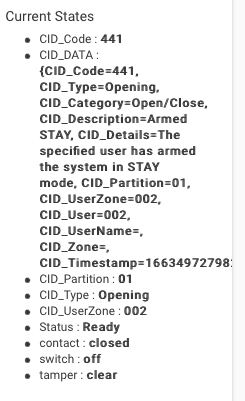
I use Honeywell Security App by Brian Wilson Honeywell Partition' device's command 'disarm' with no parameters from RM or the devices button and it sends a command to the RPi's docker app that in turn relays the disarm command to the envisalink that disarms the Vista. I also use this same Hubitat app to manage my various HSM states since I have that option activated for this Hubitat app.
Honeywell Security: Running Process Event [partition:1, alpha:****DISARMED**** Ready to Arm, state:ready, type:partition]
Honeywell Security: send command: /plugins/envisalink/disarm
Honeywell Security: Sending HSM Event to hsmSetArm: armHome (partition status: armedstay)
Honeywell Security: Partition Device: Honeywell Partition
Perhaps you can monitor the 'smartthings-nodeproxy' docker app's log messages to see if Hubitat is communication with the docker app using the following docker commands; one to restart the docker 'smartthings-nodeproxy' app and then immediately the next docker command to watch the logs. Then try the disarm command in the Hubitat's Honeywell partition device to see what is transmitted to the 'smartthings-nodeproxy' docker container.
'docker restart smartthings-nodeproxy'
'docker logs -f -n25 smartthings-nodeproxy'
Then on the Hubitat Apps page, edit your 'Honeywell Security' app and save it, so that it will communicate with the 'smartthings-nodeproxy' docker app. You should see messages in the Rpi's docker log file with the communication between Hubitat and Rpi's docker.
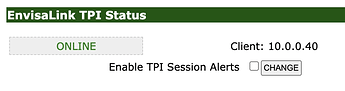
Here is my Rpi docker logs to arm and disarm the Vista. Note the log line with the 'TX > {Vista Alarm Password ****}1' which is the command that is sent to the EnvisaLink which is listening to the docker app at 10.0.0.40 (see Envisalink's Network page image below).
[2022-09-18T09:34:34.393Z] [evl3] RX < %00,01,8C08,08,00,ARMED ***STAY***You may exit now$
[2022-09-18T09:34:34.394Z] [evl3] Execute keypad_update: 01,8C08,08,00,ARMED ***STAY***You may exit now
[2022-09-18T09:34:34.396Z] [evl3] {"partitionNumber":1,"flags":{"alarm":false,"alarm_in_memory":false,"armed_away":false,"ac_present":true,"bypass":false,"chime":false,"not_used1":false,"armed_zero_entry_delay":false,"alarm_fire_zone":false,"system_trouble":false,"not_used2":true,"not_used3":true,"ready":false,"fire":false,"low_battery":false,"armed_stay":true},"userOrZone":8,"beep":"off","alpha":"ARMED ***STAY***You may exit now","dscCode":"ARMED_STAY"}
[2022-09-18T09:34:34.397Z] [evl3] {"alpha":"ARMED ***STAY***You may exit now","timer":[],"partition":1,"zones":[null,null,null,null,null,null,null,"closed",null,"closed",null,null,null,null,null,null,null,null,null,"closed"]}
[2022-09-18T09:34:34.406Z] [stnp] ::ffff:10.0.0.79 GET /plugins/envisalink/disarm
[2022-09-18T09:34:34.407Z] [evl3] TX > {Vista Alarm Password ****}1
[2022-09-18T09:34:36.894Z] [evl3] RX < %02,0100000000000000$
[2022-09-18T09:34:36.894Z] [evl3] Execute partition_state_change: 0100000000000000
[2022-09-18T09:34:36.895Z] [evl3] RX < %00,01,1C08,08,01,****DISARMED**** Ready to Arm $
[2022-09-18T09:34:36.914Z] [evl3] Execute keypad_update: 01,1C08,08,01,****DISARMED**** Ready to Arm
[2022-09-18T09:34:36.915Z] [evl3] {"partitionNumber":1,"flags":{"alarm":false,"alarm_in_memory":false,"armed_away":false,"ac_present":true,"bypass":false,"chime":false,"not_used1":false,"armed_zero_entry_delay":false,"alarm_fire_zone":false,"system_trouble":false,"not_used2":true,"not_used3":true,"ready":true,"fire":false,"low_battery":false,"armed_stay":false},"userOrZone":8,"beep":"beep 1 time","alpha":"****DISARMED**** Ready to Arm","dscCode":"READY"}
[2022-09-18T09:34:36.916Z] [evl3] {"alpha":"ARMED ***STAY***You may exit now","timer":[],"partition":1,"zones":[null,null,null,null,null,null,null,"closed",null,"closed",null,null,null,null,null,null,null,null,null,"closed"]}