I like UniFi gear... A lot. I currently manage three seperate UniFi depoyments...
My current home environment consts of...
- UniFi Dream Machine Pro
- US-24 250W PoE Switch
- US-24 Switch Non-PoE
- Flex-5 PoE Switch (detached garage)
- USW-Flex Mini (Not provisioned)
- (3) AP-AC Pro
- (1) AP-AC Mesh
- (7) UVC-G3 Cameras
- (8) UVC-G3 Flex Cameras
I also have a small deployment in my Datacenter (which is a Cisco plant) for the back-office side.. I chose this because it's easy on the budget, and the VPN is easy to configure and manage. I don't have to tie up my limited engineering resources servicing non-core functions.
- UniFi Gateway Pro-4
- US-24 250W PoE Switch
- US-24 Switch Non-PoE
- Cloud Key Gen2 Plus
And finally, at my friends campground campground I built and manage a system that covers about 1/8 of the 80 acre park. I'll be upgrading some of those components this year...
- UniFi CloudKey Gen 2
- US-8 60W PoE Switch
- UniFi Gateway (non-pro)
- (8) AP-AC Mesh APs
There are a lot of things that I really like about the ecosystem. First, the equipment is very, very reasonably priced. For example, I just took delivery on the new Flex-5, 5 port managed switch. I paid $29 plus tax and shipping.... Try going to Best Buy for a 5 port managed switch that can be powered by PoE. You can't.
For the most part everything plays very well together. My home deployment centers around two 24 port switches, one PoE, one without. This was considerably cheaper than a single 48 port PoE switch. I have a buried CAT-7 line to my detached garage connected to a Flex-5 switch and 2 UVC-G3 Flex cameras. All of that is powered off of the PoE switch in the attic of the house.
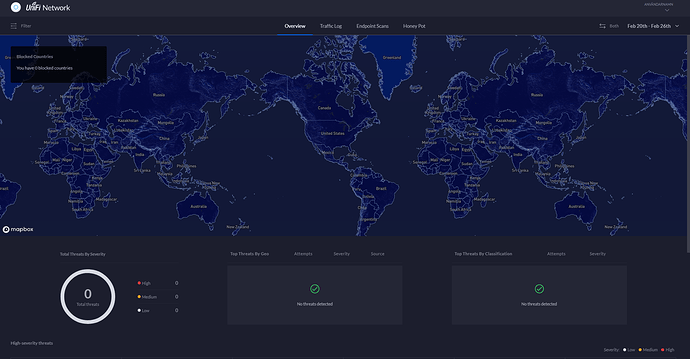
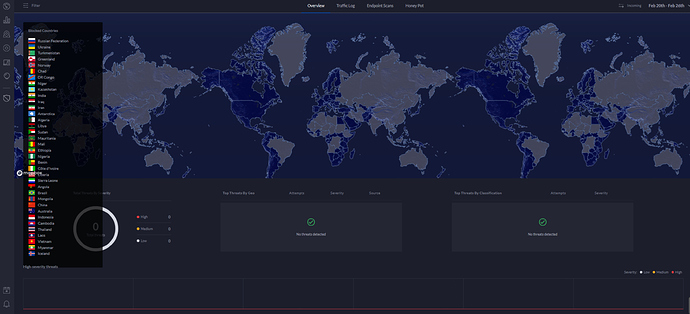
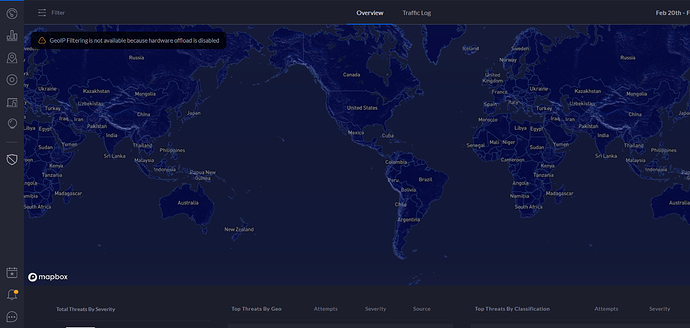
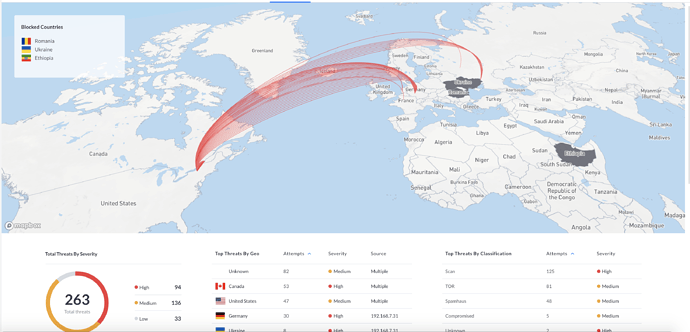
With the UDM Pro, I have most of the intrustion detection settings enabled. I'm shocked at the dozens of blocked threats that are reported daily. I have started to block some countries as a result of the concentration of these attacks.
The VPN server built into the UDM (and USG's) is a basic L2TP tunneling server. It's natively supported in Windows and Macs (including iOS devices) so no software is needed. You're not going to find the fine-grained policies available in a Cisco VPN server.. Nowhere near as close, but for a home office, or small business, it's perfect. It also makes it very easy to VPN in to manage my Hubitat hubs.
What I don't like, or issues I've encountered...
Really there's only one thing... The Dream Machine Pro... It's a disappointment that comes in a box. I have had it for almost 2 weeks and it's really beena blight on my normally positive view of Unifi. The product feels incomplete and rushed to market. There are numerous things that don't work, are limited, or glitchy. If you're comforatable with SSH logins, you can signup for early access and install the latest beta.. That improves things somewhat.
These are the issues I've run into so far...
- Out of the box, on first power and subsequent power ups, the LCD displayed a "fatal error". I had to hard reset the unit following the instructions in the community, then load the latest firmware in order to provision the unit.
- Restoring old backups fails when cloud connected. You must be connected locally.
- Dynamic DNS is broken.
- WAN 1 is a 1gbps RJ45. WAN 2 is a 10gbps SFP+.. Currently WAN 1 can only be used for primary internet. The 10G port is limited to a redundant ISP.
- WAN2 is won't autonegotiate less than a 10G connection. If you install the beta that is fixed.
- The 8 port switch does not support LACP. You're limited to a single 1gbps uplink, or provisioning multiple 1G ports for seperate VLANs.
- Firewall port mapping ranges (which work fine on the USG's) are broke. Rules that use multiple ports have to be re-created as multiple rules using a single port each.
- Protect randomly stops recording cameras for minutes at a time.
- The UniFi mobile app continuously needs to be force-quit in order to connect to the UDM. This issue doesn't happen on my cloud-key deployments.
I would avoid the UDM-Pro for now.. It's really my only complaint..
The rest of the ecosystem is pretty cool and works well. I've had no interop issues with Hubitat (i.e. port negotiation issues). I've had no WiFi inteference issues with Zigbee, despite the desnity of access points. (I have the power dialed back on each so roaming is more effective).
I think it's a good choice over the standard consumer fare.. If you're willing to spend a little extra cash and commit the extra time to get it set up and dialed in correctly.